
WEST PALM BEACH, FL – Phishing isn’t new. Spam isn’t new. Most of it is easy to spot and easier to ignore. What is new is how it’s being delivered. Recently, I experienced a more coordinated scam than usual – one that didn’t begin with an email at all. It began with a phone call – and that distinction matters more than most people realize.
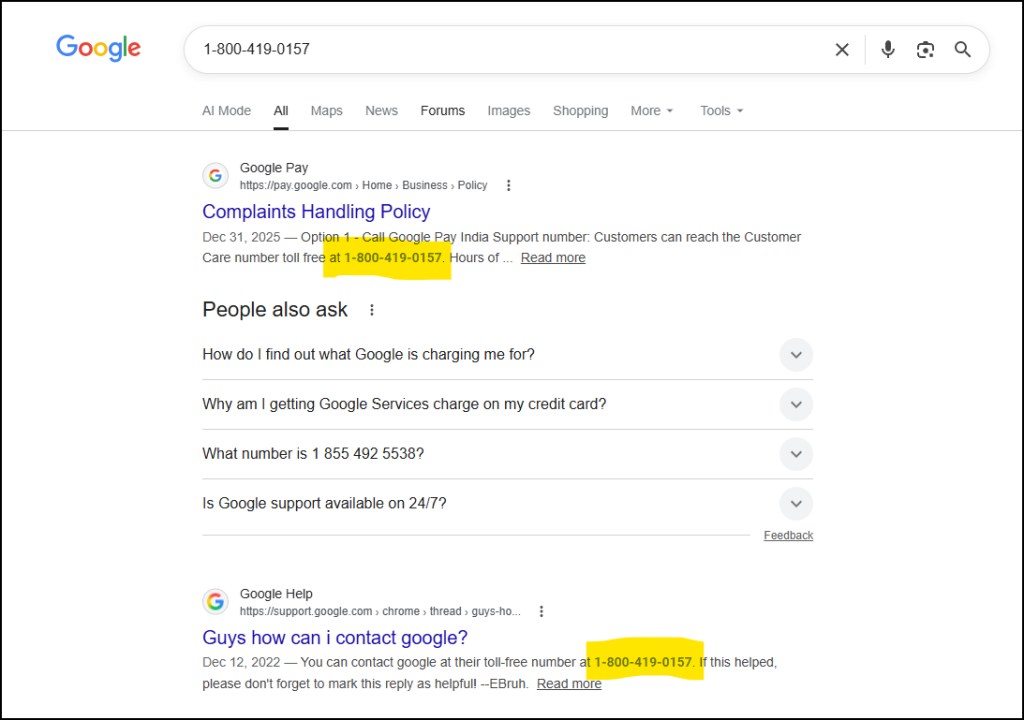
The first contact was an automated call referencing suspicious activity on my account. It mentioned a login attempt in Carson City, Nevada and prompted a response to confirm whether the activity was legitimate. The call came from 1-800-419-0157, a number that, when searched, appears associated with Google customer support.
That detail is not accidental.
On its own, that’s already a step beyond traditional phishing. You’re no longer just receiving a message – you’re being pulled into an interaction that feels connected to a real system.
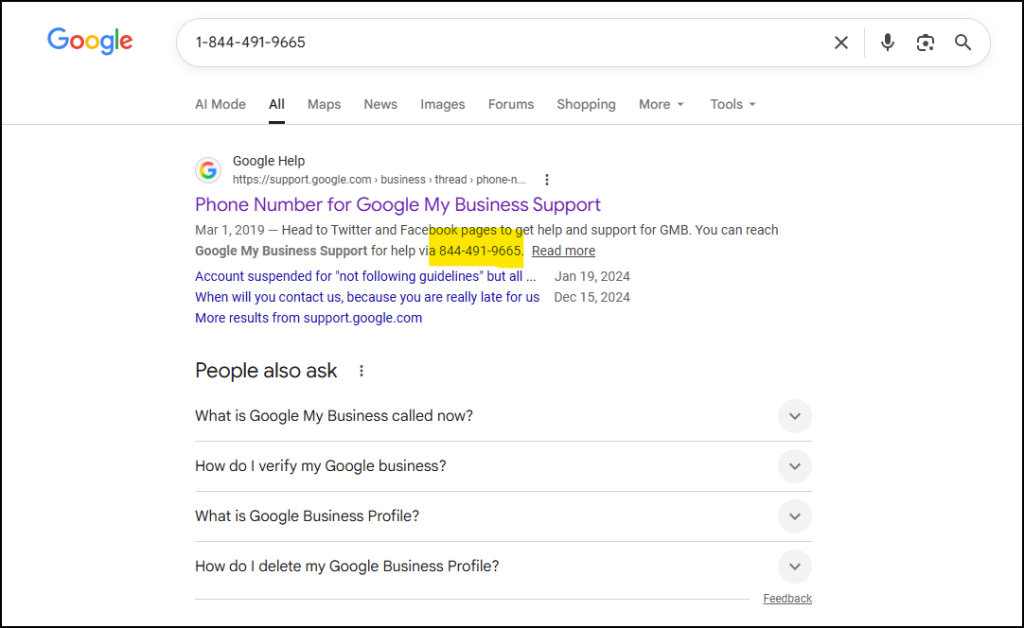
Within minutes, a second call came in. This time it was a live person, calling from 1-844-491-9665 – another number that traces back, at least on the surface, to what appears to be Google support.
This is where the attack becomes far more convincing.
The individual on the phone spoke clearly, confidently, and without hesitation. No broken English. No awkward pauses. No obvious signs of a scam operation. Just a calm, professional voice walking through what sounded like a legitimate account security issue.
He explained that someone was attempting to access my GMAIL account, referencing attempted changes to backup email settings and two-factor authentication. Everything sounded plausible. More importantly, it sounded routine – like something you would expect from a real support interaction.
Caller ID reinforced that perception. The numbers looked legitimate. The tone was professional. The scenario made sense. At that point, the interaction felt less like a scam and more like a standard escalation process. Still, I remained skeptical and told the caller as much.
He then suggested sending an email to verify his identity – and that’s where things started to fall apart.
When I checked my inbox, a message sent earlier were sitting in spam. And it looked exactly like it was: low-quality phishing attempts. Poor formatting, questionable sender domains, and nothing close to what you would expect from an actual Google communication.
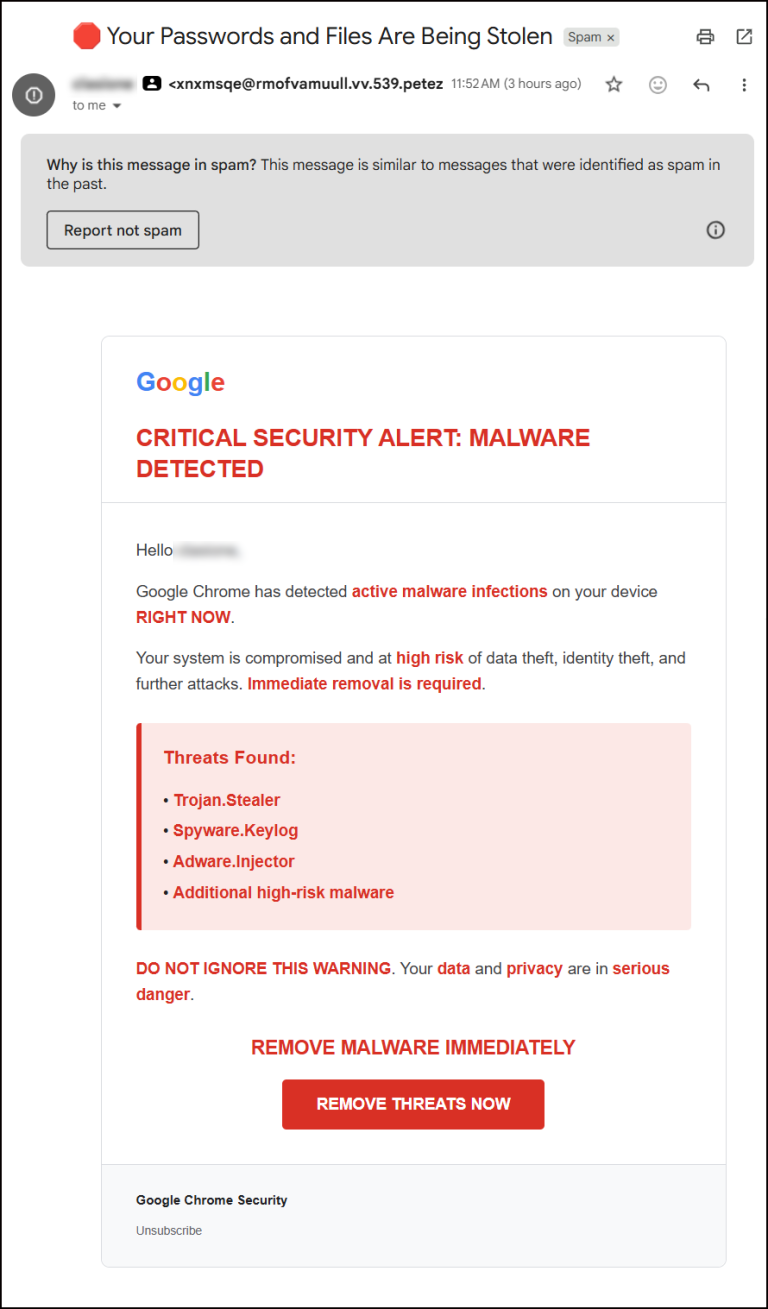
Then the real hammer came down on the caller. The email he sent while on the phone – intended to validate his identity – landed in spam.
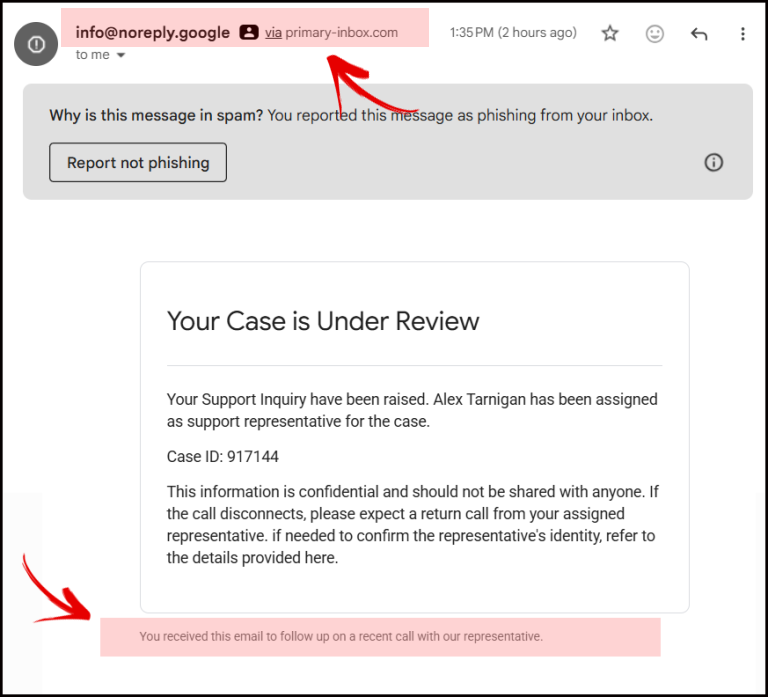
While slightly more convincing at first glance, it still exposed itself quickly: used a suspicious “.google” domain and was sent via primary-inbox.com.
At that point, it was clear where this was heading. The next step would have been to “verify” my identity via a text message. In reality, that code would have been generated by a live login attempt, allowing him to pass two-factor authentication in real time and take control of the account.
I told him I no longer needed to continue the conversation because it was clearly a scam. He immediately hung up.
Phishing used to rely on getting you to click something. Now it relies on getting you to trust someone. The phone call becomes the primary channel. The attacker controls the pace, answers questions on the fly, and adjusts based on your reactions. The email is no longer the hook – it’s just a prop.
From a strategic standpoint, this is a completely different problem. If an attacker can successfully guide someone through a conversation, the likelihood of compromise increases significantly. It’s no longer about spotting a bad link. It’s about recognizing when a situation itself is being engineered.
And for businesses, the stakes are high.
A compromised Google account doesn’t just mean access to email. It can open the door to advertising accounts, analytics data, client communications, banking systems, investment accounts, crypto wallets, cloud services, and in some cases, even domain-level controls. One successful interaction can ripple across an entire operation.
There’s also an operational detail worth noting. The emails associated with this attempt were caught by Gmail’s spam filters, which are known to be aggressive and data-driven. In contrast, Google Workspace didn’t accept the messages at all – they never reached the inbox, spam, or trash. Filtering behavior can vary depending on configuration, but it reinforces the importance of not relying solely on default protections.
The real takeaway here isn’t about email quality or spam detection. It’s about understanding where the attack is actually happening. In this case, the risk wasn’t in the inbox. It was on the phone. And that’s where most people are still unprepared.
A well-spoken voice, a believable scenario, and a number that appears legitimate – like 1-800-419-0157 or 1-844-491-9665 – can bypass the instincts people have developed over years of ignoring bad emails. It feels immediate. It feels personal. And it feels legitimate in a way that traditional phishing rarely does.
But the weakness in these attacks hasn’t changed.
The moment you slow things down and verify independently, the entire structure starts to break. The urgency loses its power, the inconsistencies become obvious, and the attacker has no choice but to disengage. That’s exactly what happened here.
The emails didn’t hold up. The story didn’t hold up. And once the script was interrupted, the call ended. Phishing hasn’t disappeared. It’s evolved. And right now, it’s calling you.

About The Author: John Colascione is Chief Executive Officer of SEARCHEN NETWORKS®. He specializes in Website Monetization, is a Google AdWords Certified Professional, authored a how-to book called ”Mastering Your Website‘, and is a key player in several online businesses.

 *** Here Is A List Of Some Of The Best Domain Name Resources Available ***
*** Here Is A List Of Some Of The Best Domain Name Resources Available ***
Leave a Reply